In our age of pervasive internet connectivity, maintaining online privacy has grown increasingly challenging. The specter of cyber threats looms large, making tools like proxies indispensable in the pursuit of anonymity. Proxies offer a glimpse into the endless possibilities of a more private browsing experience. Yet, for those demanding heightened security, entering the realm of proxychains might be the logical next step.
Basic Understanding of Proxies
At its core, a proxy server acts as an intermediary between a user’s computer and the broader internet. By rerouting web traffic through these servers, users can mask their original IP addresses, achieving a semblance of anonymity. For instance, someone might employ an Android socks5 proxy on their mobile device to ensure a private browsing session.
Proxychain: Stringing Together Multiple Proxies
A proxychain is a powerful concept that involves stringing together multiple proxies, creating a layered pathway for data transmission. Here’s a simple analogy: Imagine passing a secret note through several trusted friends before it reaches its intended recipient. Each friend is analogous to a proxy server in a chain. This sequence ensures that tracing back to the note’s origin becomes exceedingly difficult.
Multi-layer Wall: Enhancing Online Privacy with Proxychains
In today’s digital age, where data is the new currency, safeguarding one’s online privacy becomes paramount. While standard intermediaries, like Craigslist Proxies for Posting & Scraping, offer a decent layer of obscurity, the chain of proxies takes this veil of anonymity to another level. When a user harnesses the power of proxychains, they navigate the digital seas with an armada, instead of a single ship:
- Obfuscation of original IP: A basic proxy might mask your original IP, but with each additional proxy in the chain, the task of retracing steps back to the source becomes akin to finding a needle in a haystack. This multi-layer masking ensures that trackers, advertisers, or malicious actors find it almost impossible to identify the source of the traffic.
- Increased difficulty for traffic analysis: In a world where big data analytics plays a pivotal role in understanding user behavior, a proxychain becomes a conundrum for analysts. The intertwined and convoluted pathways make it challenging for any eavesdropper to understand or predict user behavior, thereby preserving user privacy.
- Layered encryption: Think of a Russian nesting doll; as one layer is unveiled, another one awaits. Similarly, as data moves from one proxy to the next, it gets encrypted multiple times. So even if a cyber miscreant manages to break one layer of encryption, they are greeted by another, making the data pilferage task Herculean.
Strong Defense: Fortifying Security Through Proxychains
- Defense against malicious entities: A malefactor aiming to infiltrate a user’s system will grapple with multiple protective layers.
- Protection against compromised proxies: Even if one server in the chain is compromised, subsequent servers ensure data remains cloaked.
- Mitigating risks of data leakage: Multiple encryption layers ensure that, even if data is intercepted, it remains an indecipherable puzzle.
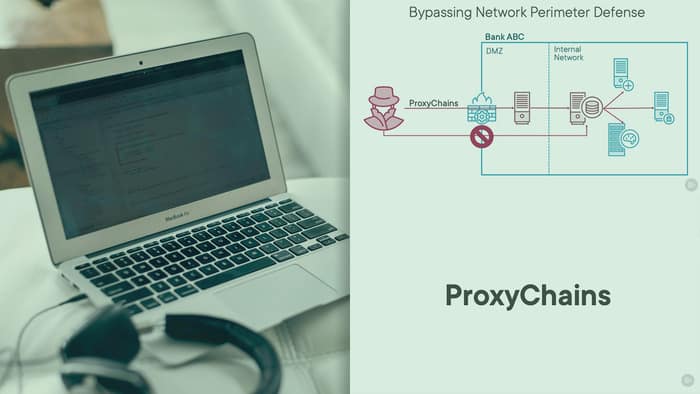
How to Implement a Proxychain: Practical Solutions
For the tech-savvy individual or the privacy-focused user, the theoretical understanding of proxychains is not enough. Actionable insights into how one can set up and utilize the chain of proxies are necessary. Several tools and platforms cater to this very need:
- ProxyChains: This open-source tool, predominantly designed for Linux aficionados, offers immense flexibility. It allows users to mix different proxy types in the same chain, ensuring that the digital journey is as intricate as one desires. The tool delivers a user-defined list of proxies chained together and allows TCP and DNS tunneling through proxies, ensuring uninterrupted access to the sources from behind a restrictive firewall. Moreover, with an active community backing it, issues and glitches get addressed swiftly.
- Tor: The Onion Router, commonly known as Tor, is not just a tool but an emblem of online privacy. While many perceive Tor as a standalone privacy tool, it inherently employs a variant of proxy chaining. Data transits through multiple, random volunteer-operated servers before reaching its destination. For users seeking an out-of-the-box solution with minimal setup, Tor presents an ideal choice.
Remember, while these tools offer tremendous utility, the onus remains on the user to pick reputable proxy servers within the chain. A chain, after all, is only as strong as its weakest link. And in the realm of digital privacy, a compromised proxy can be the Achilles’ heel.
The Flip Side of the Coin: Potential Drawbacks and Limitations
As with any technological marvel, proxy chains are not without their share of imperfections. Being aware of these limitations ensures that users can make informed decisions and mitigate risks:
- Reduced browsing speed: The digital odyssey of data, from the user to the destination via numerous proxies, is nothing short of epic. But this grand journey, while bolstering privacy, comes at the cost of speed. Each proxy introduces latency, leading to discernibly slower browsing experiences.
- Risk of over-relying on proxychains: A common pitfall for many is considering the chain of proxies as the ultimate shield against all online threats. While they enhance anonymity the chain should complement, not replace, other security measures. Tools like VPNs, end-to-end encrypted messaging apps, and secure browsers should be part of one’s digital defense arsenal.
- Possible configuration errors: The power of proxy chains lies in their complexity. However, this complexity can be a double-edged sword. Improper configurations can introduce vulnerabilities or even render the chain ineffective. Regular audits, updates, and an understanding of the intricacies are crucial to maintaining the efficacy of the proxy chain.
Comparing Proxychains to Other Privacy Tools
While chains of intermediaries are compelling, it’s worth juxtaposing them against other privacy tools:
- VPNs vs. Proxychain VPNs provide a singular, encrypted tunnel for web traffic. They’re generally faster but might not offer the layered obfuscation of a proxy chain.
- Dedicated IP Proxies vs. Proxychain: The former offers a static IP address, ideal for tasks that require consistent IPs, while a chain of proxies emphasizes undiluted anonymity.
Final Thoughts
As the digital landscape continues to evolve, the quest for impeccable privacy and security remains ceaseless. Proxychains, with their layered approach, present a fascinating solution in this ever-complicated cyberspace. For those seeking an unadulterated blend of anonymity and protection, the chain of proxies might very well be the key to unlocking a safer, more private digital existence.